KeyStore and TrustStore
- Technically a KeyStore and a TrustStore are of same. They just serve different purposes based on what they contain.
- A KeyStore is simply a database or repository or a collection of Certificates or Secret Keys or key pairs. When a KeyStore contains only certificates, you call it a TrustStore.
- When you also have Private Keys associated with their corresponding Certificate chain (Key Pair or asymmetric keys), it is called a KeyStore.
- Your truststore will be in your JAVA_HOME—> JRE –>lib—> security–> cacerts
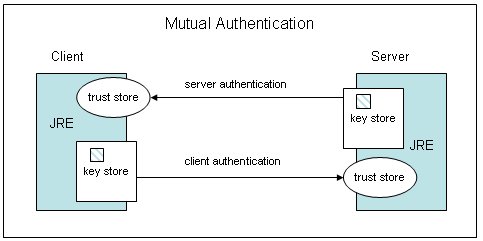
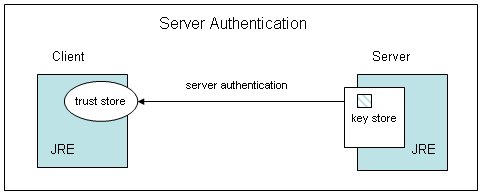
- ‘cacerts’ is a truststore. A trust store is used to authenticate peers. A keystore is used to authenticate yourself in mutual authentication
- cacerts is where Java stores public certificates of root CAs. Java uses cacerts to authenticate the servers.
Keystore is where Java stores the private keys of the clients so that it can share it to the server when the server requests client authentication. - Keystore is used to store private key and identity certificates that a specific program should present to both parties (server or client) for verification.
Truststore is used to store certificates from Certified Authorities (CA) that verify the certificate presented by the server in SSL connection. - Mutual authentication requires Keystore and Truststore whereas Server-Client authentication requires truststore to store Certificates from CA.
List the content of your keystore file
keytool -v -list -keystore .keystore
specific alias, you can also specify it in the command
keytool -list -keystore .keystore -alias foo
Importing Certificate to Truststore
keytool -import -trustcacerts -keystore $JAVA_HOME/jre/lib/security/cacerts -storepass changeit -alias Root -import -file Trustedcaroot.txt